We're publishing a full sweep of our own stack. One account, the same IP per region, four protocols on each, all measured from a single European client. Raw numbers: throughput, latency, SOCKS5 UDP behavior, header leaks.
Methodology, numbers, and conclusions below.
Why we ran this
Sooner or later every customer asks: "Which protocol should I pick?" The standard answer across the industry is marketing copy: "HTTPS-secure", "SOCKS5-flexible", "Shadowsocks-stealth". No numerical differences. No admission of where a particular vendor falls short.
We had test data covering all our endpoints, so we put it in one place. Why we publish it:
- anyone can run the same commands and verify the result on our stack or on a current provider;
- it helps our internal work — we see weak spots and where to invest;
- the format itself is what the industry needs: numbers > promises.
Methodology
Test client: our own server in Europe. All requests over IPv4, to rule out IPv6 routing effects.
Tools:
curl 8.5.0— for HTTP/HTTPS/SOCKS5 TCPss-local(shadowsocks-libev 3.3.5) — for Shadowsocks- raw Python sockets — for SOCKS5 UDP ASSOCIATE
openssl s_client— to verify the TLS handshake to the HTTPS proxy
Metrics:
- Throughput —
https://speed.cloudflare.com/__down?bytes=10000000, 10 MB file, recorded via curl'sspeed_download - Latency — TTFB to
https://www.google.com/generate_204, median of 5–10 runs - SOCKS5 UDP RTT — DNS query (A example.com) to 8.8.8.8:53 through the UDP relay, median of 5 runs
- Anonymity — body of
httpbin.org/headers, looking forVia,X-Forwarded-For,X-Real-IP,Forwarded,Proxy-Connection
Throughput
Tests run from a European client. NL and DE are closest, UA is at comparable distance, US is farthest.
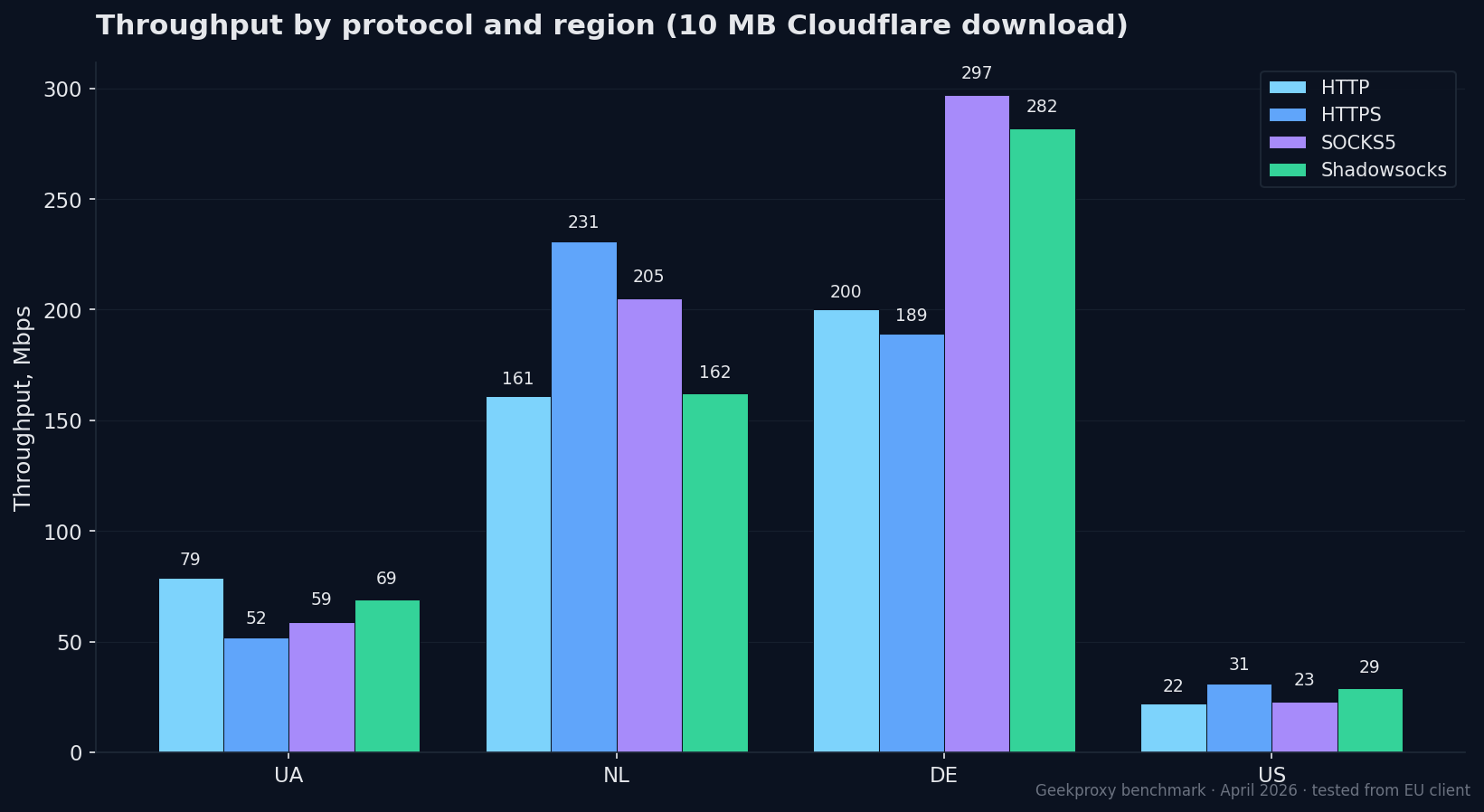
| Protocol | UA | NL | DE | US |
|---|---|---|---|---|
| HTTP | 79 Mbps | 161 Mbps | 200 Mbps | 22 Mbps |
| HTTPS | 52 Mbps | 231 Mbps | 189 Mbps | 31 Mbps |
| SOCKS5 TCP | 59 Mbps | 205 Mbps | 297 Mbps | 23 Mbps |
| Shadowsocks | 69 Mbps | 162 Mbps | 282 Mbps | 29 Mbps |
What stands out:
- DE is the fastest PoP for a European client. 297 Mbps on SOCKS5, 282 on Shadowsocks. NL is close (231 on HTTPS).
- The UA endpoint is 2–4x slower than NL/DE despite comparable physical distance. That's the PoP's upstream link, not the protocol.
- US from a European client lands at the expected 22–31 Mbps, capped by transatlantic latency and the destination throughput. A US-client test would give the honest US-locale picture.
Latency
TTFB to google.com through each protocol, median of 5–10 runs.
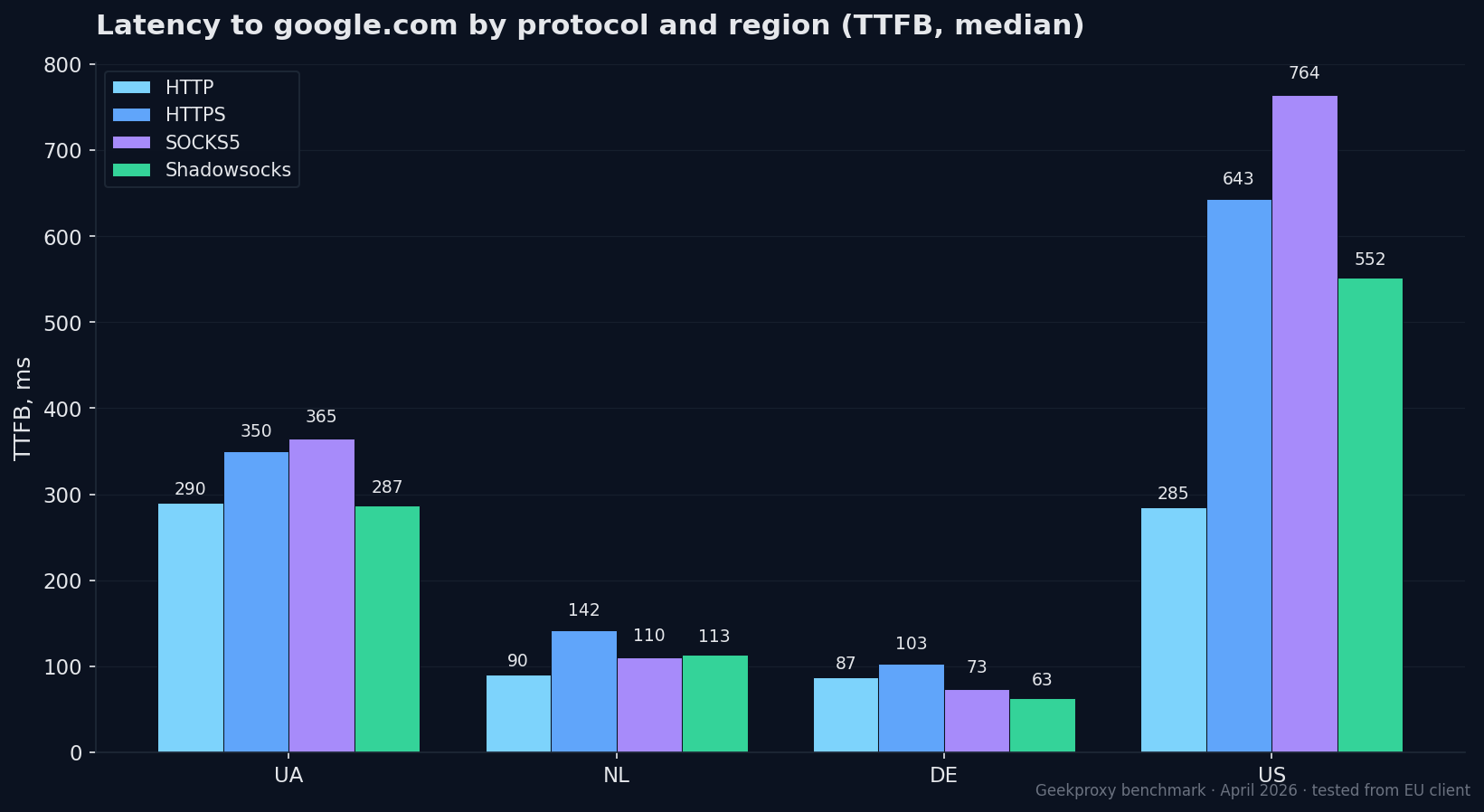
| Protocol | UA | NL | DE | US |
|---|---|---|---|---|
| HTTP | 290 ms | 90 ms | 87 ms | 285 ms |
| HTTPS | 350 ms | 142 ms | 103 ms | 643 ms |
| SOCKS5 TCP | 365 ms | 110 ms | 73 ms | 764 ms |
| Shadowsocks | 287 ms | 113 ms | 63 ms | 552 ms |
What matters:
- HTTPS proxy adds ~100–200 ms of latency on a fresh connection because of the TLS handshake to the proxy. With keep-alive, the overhead disappears after the first request.
- HTTP is the fastest by latency, as expected (no TLS wrapping).
- DE leads again: 63 ms TTFB on Shadowsocks, almost like a direct connection.
- The US numbers from a European client confirm the methodology: 643 ms for HTTPS is the transatlantic TLS handshake plus connection setup to the destination.
SOCKS5 UDP — the part most competitors silently fail
UDP in SOCKS5 is the UDP ASSOCIATE command from RFC 1928. Most "SOCKS5 proxies" in the industry don't actually support it: TCP tests with curl pass, but DNS over UDP, QUIC/HTTP3, WebRTC, Telegram bots, game protocols — silently fail, with no useful error.
We ran a raw test: ASSOCIATE → DNS query (A example.com) to 8.8.8.8:53 through the proxy's relay port.
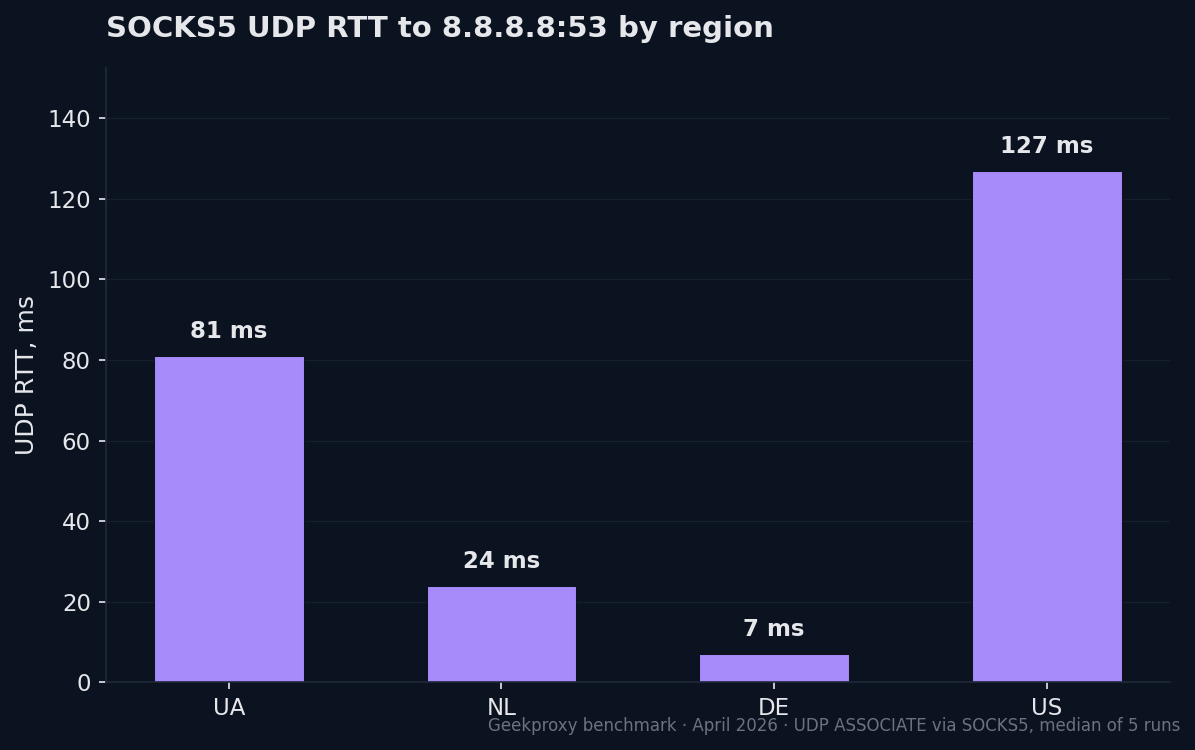
| PoP | UDP RTT min | median | max |
|---|---|---|---|
| UA | 70 ms | 81 ms | 98 ms |
| NL | 14 ms | 24 ms | 26 ms |
| DE | 6 ms | 7 ms | 10 ms |
| US | 123 ms | 127 ms | 128 ms |
Also: 19 out of 19 queries through a single association completed without loss over 5 seconds. UDP can target multiple destinations through the same association (we verified with 8.8.4.4) — the relay isn't pinned to one target. That matters when a bot needs to talk to several UDP services in a single session.
Anonymity audit
All 16 combinations (4 PoP × 4 protocols) checked for header and DNS leaks.
Headers. Through httpbin.org/headers, the destination sees only Accept, Host, User-Agent, X-Amzn-Trace-Id across all 16. No Via, no X-Forwarded-For, no X-Real-IP, no Forwarded, no Proxy-Connection. From the destination's perspective, a request is indistinguishable from a direct one. Elite (L1) anonymity across all four protocols.
DNS. A query to a non-existent domain *.example.invalid through the proxy returns a proxy error (CONNECT 503), not our local NXDOMAIN. Resolution happens on the proxy side. Our DNS doesn't leak.
TL;DR
- HTTP, HTTPS, SOCKS5 (with UDP), Shadowsocks all work on every PoP across all 16 combinations.
- The advertised exit IP matches the actual exit in every case.
- Header leaks: 0 out of 16. DNS resolution on the proxy side.
- Best European PoP for speed and latency: DE.
- HTTPS proxy: valid TLS 1.3 + Let's Encrypt cert on every endpoint, verifiable with
openssl s_client. - The US endpoint will give honest numbers only when tested from a US client.